In maintaining a cybersecurity program, compliance with best practices and industry standards has always been the name of the game. Whether it be compliance with government compliance frameworks such as the Cybersecurity Maturity Model Certification (CMMC), industry standard frameworks such as ISO 27001, or just compliance with internal security policies, an organizations’ cybersecurity resilience is only as good as its weakest link. To illustrate this point, the Identity Theft Resource Center identified some of the most common causes of data breaches, namely due to employee error (70%), unauthorized access due to poor access control implementations (13%), and accidental web exposure due to server misconfiguration (12%). If over half of all data breaches are caused human error and a quarter are caused by server misconfiguration or poor access control implementations, then perhaps the biggest statistical threat to businesses is not necessarily from APTs with continuously evolving tactics, but from inconsistently practiced security fundamentals that undermine the strength of a security program and are often missed by traditional approaches to compliance.
Critically, a compliance program requires automated and accurate visibility into asset inventory, the ability to track KPIs, and leadership with a culture that reinforces the need for continuous improvement. Effectively tracking and managing cybersecurity performance is critical in maintaining compliance efforts because it allows decision-makers to have the best possible understanding of the weak points in their cybersecurity program. This allows for targeted improvements on exactly which performance metrics are below the satisfactory level dictated by the governing compliance standards, whether they be governmental, industry standard frameworks, or internal security guidelines. Additionally, having a compliance process in place creates a large base of documented evidence of compliance that is invaluable for internal and third-party audits.
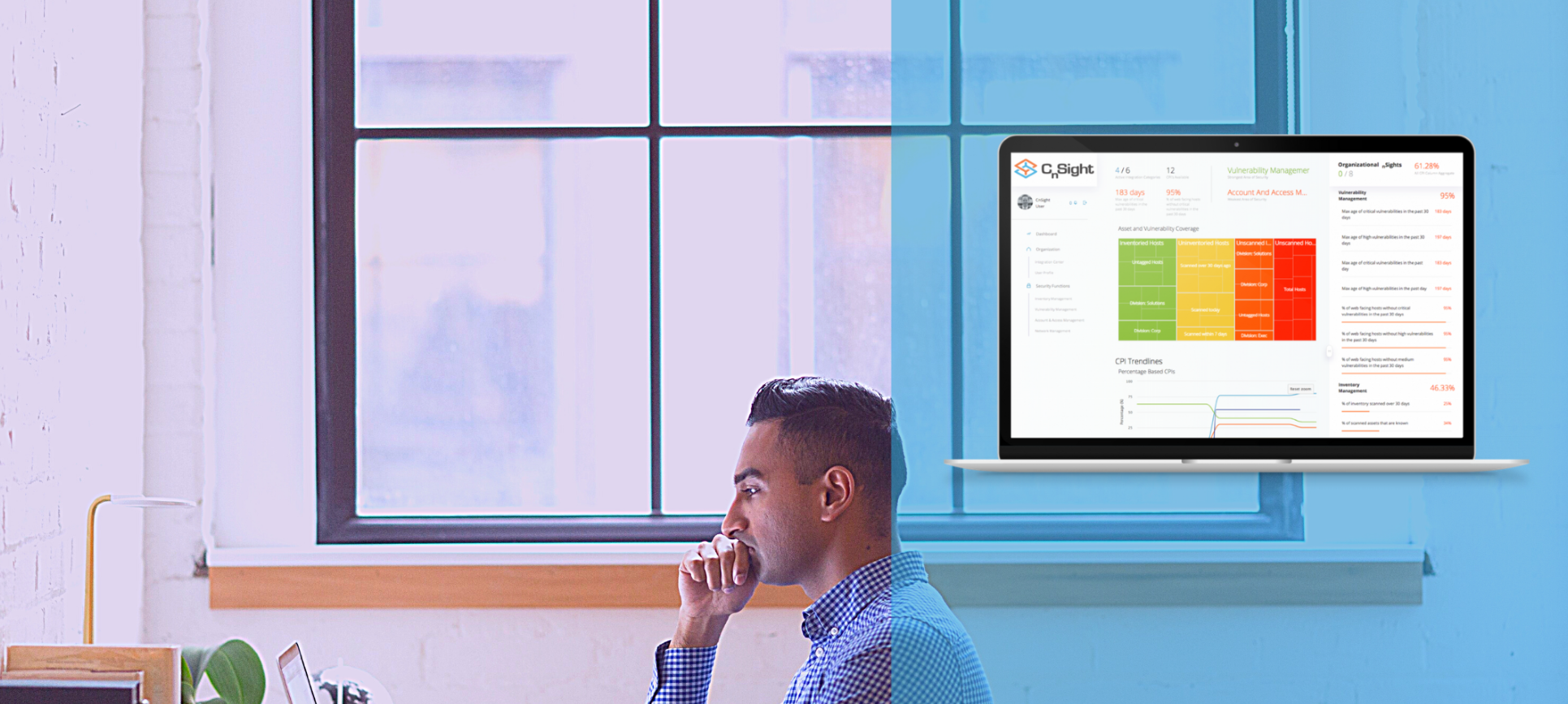
Maintaining an effective compliance program is not an easy to task, but there are tools that make it more manageable. A compliance dashboard is one of the best ways to do that, since it aggregates performance tracking and compliance data into an easily digestible format for easy comprehension by key decision-making leadership. When key decision-making executives can see the tangible effects of their investment in the organization’s cybersecurity structure, it allows for much more targeted and meaningful spending towards ensuring complete organizational compliance. Instead of throwing money at the problem and hoping it sticks, it becomes possible to methodically target every security measure that has the highest impact on getting an organization closer to full compliance. This also has the added benefit of reducing risk while lowering overall spending on inefficient security improvements.
Compliance is a process that requires diligent adherence to continuous improvement, the ability to track performance KPIs, and continuous visibility into the day-to-day operations of your team. With modern compliance tracking tools shoring up a lot of the gaps in traditional compliance programs, a compliance dashboard lowers the base difficulty of maintaining compliance standards. Tools that automate the tracking of cybersecurity performance KPIs, such as CnSight, give key insights into asset inventories, and create easily digestible reports that empower key decision-making individuals in reducing risk and ensuring organizational compliance. While these tools are only the first step, they establish a good baseline to build a cybersecurity program that values compliance to industry best practices and relevant governmental standards.